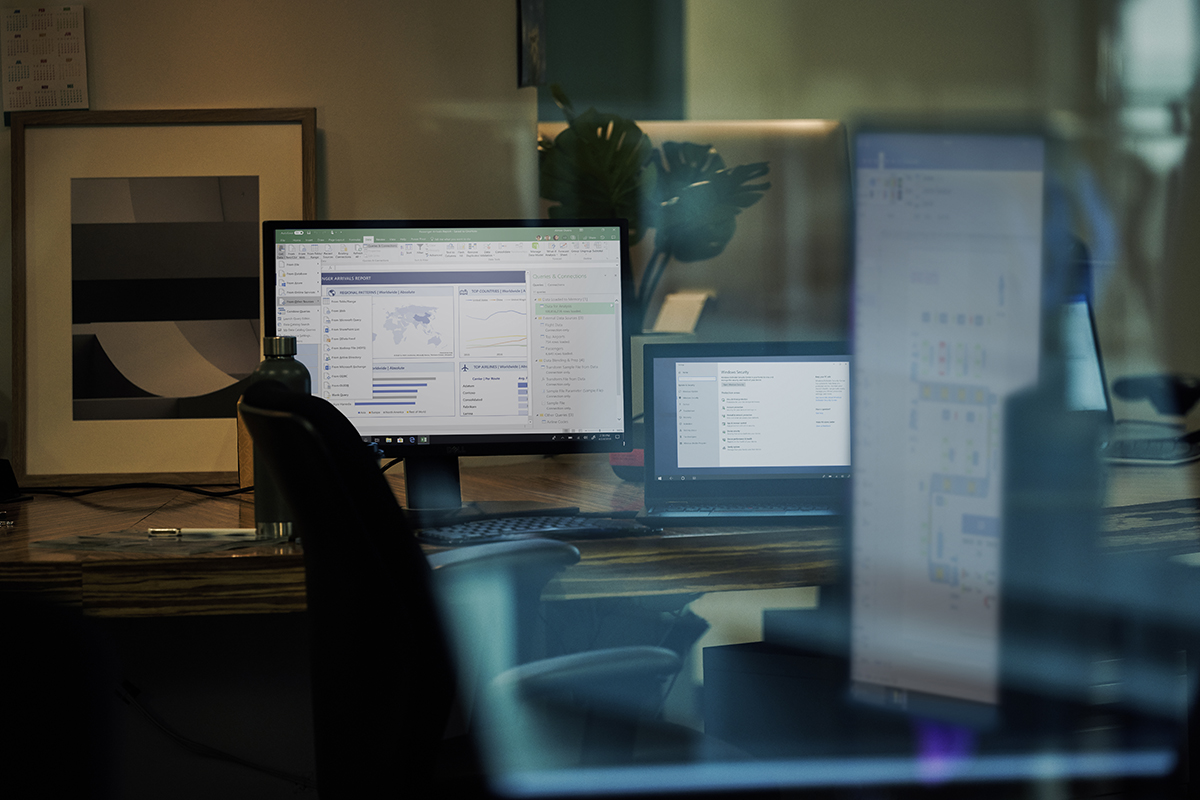
Threat actors
Microsoft actively discovers and tracks threat actors across observed state-sponsored, ransomware, and criminal activities. Get insights from the 60 nation-state actors, 50 ransomware groups, and hundreds of other attackers we’ve tracked.
Refine results
Topic
Products and services
Publish date
-
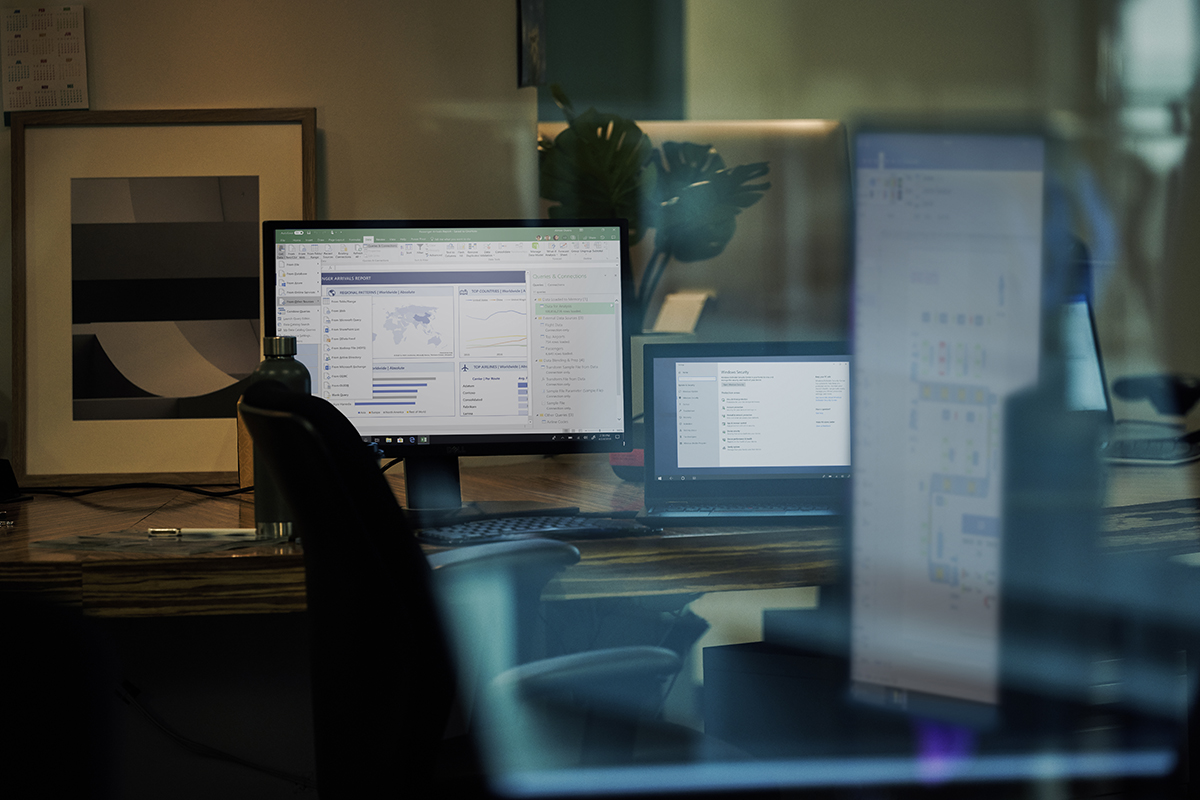 We have recently expanded the integration of Antimalware Scan Interface (AMSI) with Office 365 to include the runtime scanning of Excel 4.
We have recently expanded the integration of Antimalware Scan Interface (AMSI) with Office 365 to include the runtime scanning of Excel 4. -

GoldMax, GoldFinder, and Sibot: Analyzing NOBELIUM’s layered persistence
Microsoft has identified three new pieces of malware being used in late-stage activity by NOBELIUM – the actor behind the SolarWinds attacks, SUNBURST, and TEARDROP. -

New Security Signals study shows firmware attacks on the rise; here’s how Microsoft is working to help eliminate this entire class of threats
The March 2021 Security Signals report showed that more than 80% of enterprises have experienced at least one firmware attack in the past two years, but only 29% of security budgets are allocated to protect firmware. -

Automating threat actor tracking: Understanding attacker behavior for intelligence and contextual alerting
A probabilistic graphical modeling framework used by Microsoft 365 Defender research and intelligence teams for threat actor tracking enables us to quickly predict the likely threat group responsible for an attack, as well as the likely next attack stages. -

Microsoft discovers threat actor targeting SolarWinds Serv-U software with 0-day exploit
Microsoft has detected a 0-day remote code execution exploit being used to attack SolarWinds Serv-U FTP software in limited and targeted attacks. -

Combing through the fuzz: Using fuzzy hashing and deep learning to counter malware detection evasion techniques
A new approach for malware classification combines deep learning with fuzzy hashing. -

When coin miners evolve, Part 2: Hunting down LemonDuck and LemonCat attacks
LemonDuck is an actively updated and robust malware primarily known for its botnet and cryptocurrency mining objectives. -

FoggyWeb: Targeted NOBELIUM malware leads to persistent backdoor
In-depth analysis of newly detected NOBELIUM malware: a post-exploitation backdoor that Microsoft Threat Intelligence Center (MSTIC) refers to as FoggyWeb. -

Threat actor DEV-0322 exploiting ZOHO ManageEngine ADSelfService Plus
Microsoft has detected exploits being used to compromise systems running the ZOHO ManageEngine ADSelfService Plus software versions vulnerable to CVE-2021-40539 in a targeted campaign. -

HTML smuggling surges: Highly evasive loader technique increasingly used in banking malware, targeted attacks
HTML smuggling, a highly evasive malware delivery technique that leverages legitimate HTML5 and JavaScript features, is increasingly used in email campaigns that deploy banking malware, remote access Trojans (RATs), and other payloads related to targeted attacks. -

Evolving trends in Iranian threat actor activity – MSTIC presentation at CyberWarCon 2021
Over the past year, the Microsoft Threat Intelligence Center (MSTIC) has observed a gradual evolution of the tools, techniques, and procedures employed by malicious network operators based in Iran.